Complete Guide: Internet of Things (IoT) Update Management
TL;DR
- 2026 IoT update management spans three layers: firmware (OS/kernel), containers (apps in Docker), and AI models (neural-network weights for Edge AI).
- Prevent bricked devices with A/B partitioning. Updates install to the inactive slot. On boot failure the device reverts to the previous stable version.
- Never update the whole fleet at once. Use canary deployment: release to 1%, then 10%, then the remaining 89%. Catches bugs before fleet damage.
- Save bandwidth and battery with delta updates — only the binary diff, not the full image. Use MQTT 5 or LwM2M for constrained devices.
- Security updates are now a regulatory requirement under the EU Cyber Resilience Act. Cryptographically sign every update. Use digital twins for state recovery.
The number of connected devices continues to grow, and forecasts for 2030 indicate fleets at a scale where manual operations are no longer feasible. In 2026, IoT update management is shaped by Edge AI on devices, stricter product security rules, and newer connectivity standards.
It’s not enough to simply build and implement an IoT system; companies need to manage and maintain it. An essential part of maintenance is the updating process, which adds new software features, improves performance, fixes bugs, and patches security issues. However, deploying a new update across all IoT devices in a system is complex and requires a well-defined update process to ensure system integrity and resilience. In this article, we discuss IoT device management and provide guidelines and best practices for update management that you can apply to your process.
What is IoT update management and device management?
IoT device management is the broad ecosystem of administrative processes that keep the fleet operational. This includes:
- Monitoring and tracking: Real-time visibility into device states and connectivity status.
- Configuration: Remote troubleshooting and adjusting settings without physical access.
- Diagnostics: Assessing hardware health and performance metrics.
IoT update management is a specialized, critical subset of this ecosystem. It’s the mechanism responsible for the device’s lifecycle evolution that deploys code changes to fix bugs, introduce new features, patch security vulnerabilities, and update on-device AI models. While device management keeps the lights on, update management ensures the system remains secure and competitive over time.
IoT update management in 2026
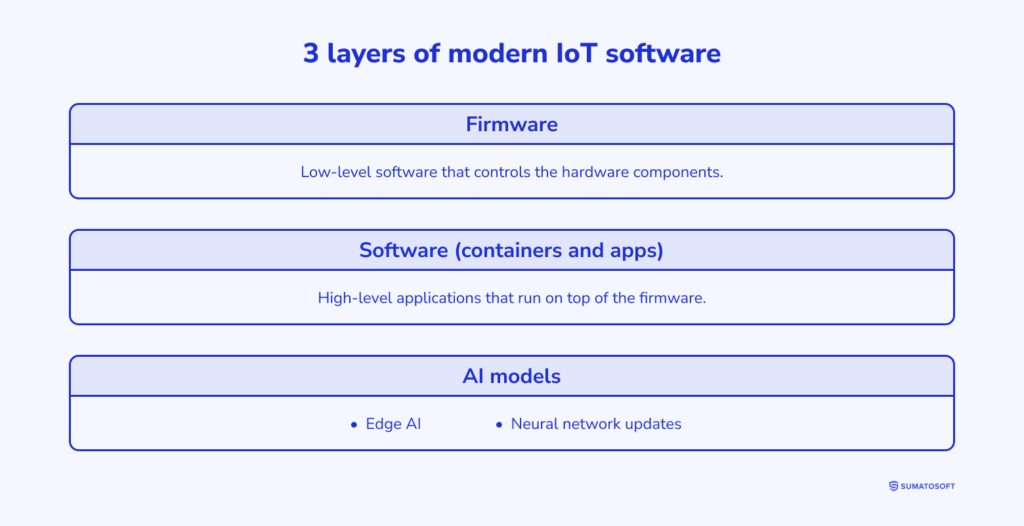
IoT update management orchestrates the deployment of data packages to remote devices to ensure their integrity and functionality. In 2026, this process has become more granular. To understand it, we must define the three distinct layers of modern IoT software:
- Firmware: The low-level software (like the RTOS or Linux Kernel) that controls the hardware components. Updates here are critical but risky, often requiring a full system reboot.
- Software (containers and apps): High-level applications that run on top of the firmware. Modern devices often use containerization (e.g., Docker), allowing you to update a specific business application without rebooting the entire device.
- AI models: With the rise of Edge AI, updates now frequently involve shipping new neural network weights to correct model drift without touching the OS or apps.
Updates are typically delivered over-the-air (OTA), eliminating the need for physical access. There are two primary architectural approaches to this:
- Direct-to-cloud: Devices download updates directly from a central distribution server. This is common in consumer electronics but requires every device to have a strong internet connection.
- Gateway-mediated: A local gateway downloads the update once and distributes it to a group of local sensors. This is essential for industrial fleets or low-power sensors that lack strong embedded security or high-bandwidth connectivity.
Regardless of the method, the process today is driven by compliance. In many regions, providing guaranteed security updates is no longer optional but a regulatory requirement under laws like the EU Cyber Resilience Act.
Why you should pay attention to IoT update management
Go back to 2017. Airbnb used smart locks on apartment doors for flats on Airbnb’s platform. Smart locks were paired with a mobile app, providing remote access to lock control. No keys were required; guests could unlock the front door via the app.
However, some doors stopped responding to commands after the lock firmware received updates. Guests lost the opportunity to open doors from their smartphones and had to use special emergency keys. The lock vendor couldn’t fix the problem remotely. It was necessary either to return the locks to the vendor or ship a replacement lock. Either way, the vendor needed 5-7 days to resolve this issue in the first scenario, and shipping a replacement took 14-18 days.
That happened because the vendor accidentally included the subset of first-generation locks in the update group, which were not compatible with the new updates. Fortunately, the vendor resolved this critical issue.
Effective IoT update management helps to avoid such unpleasant situations. So let’s discuss the meaning of the term effective IoT update management and how you can improve your current IoT update process.
IoT update management process in 8 steps
The challenge of IoT update management is establishing a workflow that balances speed and safety. While every architecture is unique, the following framework ensures resilience across both consumer and industrial fleets.
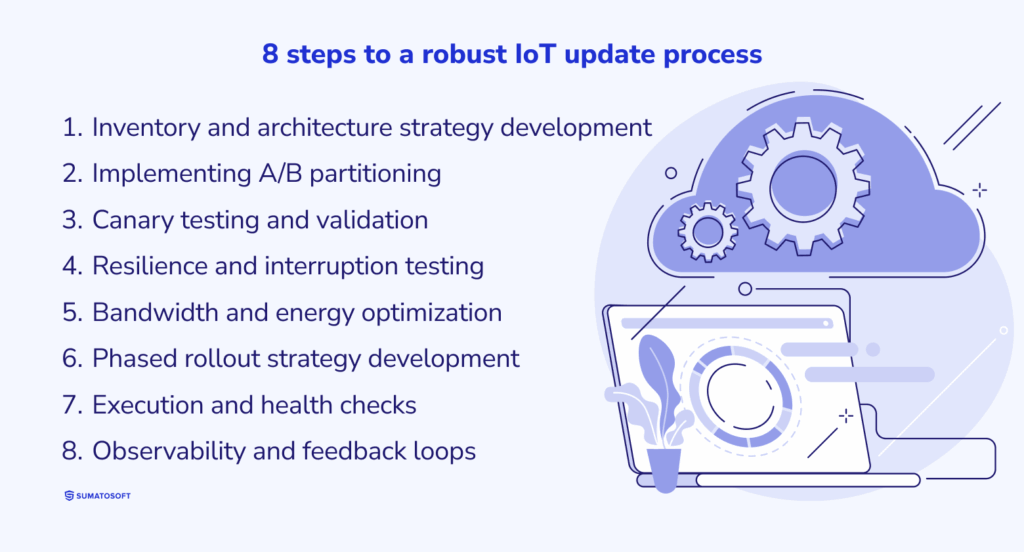
Step 1: Inventory and architecture strategy development
Before a single line of code is deployed, you must have granular visibility into your fleet. This involves generating a dynamic Software Bill of Materials (SBOM) to track dependencies and selecting the appropriate distribution method. Broadly speaking, distribution strategies fall into two categories: Gateway-Mediated and Direct-to-Cloud. The former is preferable for industrial sensors that require strict local security and bandwidth optimization, whereas the latter suits consumer devices that rely on standard Wi-Fi or 5G RedCap connections. At this stage, you must also define upgrade paths for distinct software layers, separating OS updates from containerized application patches.
Step 2: Implementing A/B partitioning (dual banking)
In modern IoT design, traditional backups are replaced by A/B partitioning. The device storage is divided into two slots: active and inactive. The update is downloaded to the inactive slot while the device continues running. This ensures atomic updates: the device transitions to the new version only after a verified boot. If the new system fails to initialize, the bootloader automatically reverts to the previous stable slot, eliminating the risk of bricking devices due to power loss or corruption.
Step 3: Canary testing and validation
Deploying untested code to thousands of devices is negligent. Define a canary group, i.e., a representative subset of devices identical in hardware and network constraints to your main fleet. Testing must go beyond basic functionality. In the era of AIoT, you must validate that the update does not degrade on-device ML model performance (model drift). Once the canary group confirms stability, delete the test artifacts and prepare for broader rollout.
Step 4: Resilience and interruption testing
Network instability is a feature of IoT, not a bug. Your testing protocol must simulate worst-case scenarios: power cuts during installation, sudden signal loss, and corrupted payloads. The update agent must be able to resume downloads from the last byte rather than restarting, preserving battery life and data quotas.
Step 5: Bandwidth and energy optimization (green updates)
Updates are resource-intensive. To mitigate impact, implement delta updates, i.e., transmitting only the binary difference between versions rather than the full image. This can reduce payload size by up to 90%. Furthermore, scheduling should be context-aware. Industrial fleets might update during scheduled downtime, whereas battery-powered consumer devices should prioritize updates only when charging or when renewable energy availability is high, aligning with modern green IT standards.
Step 6: Phased rollout strategy development (ring deployment)
Avoid “Big Bang” deployments. Divide your fleet into concentric rings: starting with 1% (early adopters), moving to 10%, and finally the remaining 89%. By adhering to this practice, you contain the blast radius of any unforeseen bugs. If an error is detected in the 10% group, the rollout automatically pauses, protecting the majority of the fleet.
Step 7: Execution and health checks
Initiate the deployment. The process should be automated: the management platform pushes the command, monitors the successful handshake, and verifies the new version hash. Crucially, the system must perform a post-update health check (self-test) before reporting success.
Step 8: Observability and feedback loops
Deployment does not end at installation. The system must transition into a hyper-care monitoring phase. Devices should continuously ship telemetry regarding error rates, reboot loops, and application latency. This feedback loop is essential not just for troubleshooting, but for informing the development of the next software iteration.
Best practices of IoT update management
Make a long-term support agreement with manufacturers
IoT devices consist of different parts that might break. The option to replace a broken part quickly is necessary to build a robust IoT system.
Block the option of direct firmware updates from manufacturers
Since manufacturers also provide updates for microcontrollers and embedded sensors, they can send updates directly to the IoT components they made. However, uncentralized update deployment may lead to errors and conflicts in IoT devices. Therefore, IoT update management should also include the management of updates from third parties.
Use cryptographic validation
Security patches help devices to stay protected from malicious software. All system images of IoT devices should be protected with a cryptographic key, and any software and firmware installation shall be permitted only after the validation procedure. Each firmware update must be digitally signed.
Provide a stable, secure end-to-end connection during the update process
This step helps secure your IoT network from man-in-the-middle attacks.
Small packages of updates are better than one big update image
It’s much easier to manage IoT updates when they are split into small pieces.
Documentation may look excessive, but it’s necessary
Maintain documentation of the update process and any issues that may have arisen. This will help troubleshoot future problems and ensure that the update process is transparent and efficient.
Don’t get confused with version control
Maintain a version control system that tracks changes and their versions, making it easier to troubleshoot issues as they arise.
Use efficient transport standards (MQTT 5 & LwM2M)
Bandwidth efficiency is critical. Broadly speaking, we distinguish between signaling and payload transport. MQTT 5.0 is the industry-standard control-plane protocol for notifying devices of available updates with minimal overhead. It supports advanced features like “Shared subscriptions” for load balancing large fleets. LwM2M (over CoAP) is the preferred choice for highly constrained devices operating on metered networks like NB-IoT. Unlike raw CoAP, LwM2M provides a standardized device management architecture that enables block-wise transfer of firmware images even over unreliable UDP.
Pros and cons of implementing IoT update process
There are some cases when IoT updates are necessary, such as patching security vulnerabilities. But is it necessary to implement the IoT update process when there are no security issues?
| Pros | Cons |
|---|---|
| Devices become less vulnerable to security threats | Poorly tested updates may lead to device failure |
| Improved user experience for users of personal smart devices | An IoT update management platform is a complex, costly system |
| Fewer bugs and errors | Update management is a resource-intensive process |
| IoT fleet gets new features and possibilities | The new update may badly affect the device’s performance or the correctness of its work |
| The latest update may result in better performance | Low network bandwidth can become a serious challenge for deploying a huge update package |
Essential tools for IoT update management
The market in 2026 is divided into three distinct categories: comprehensive cloud suites (hyperscalers), specialized fleet operations platforms, and observability tools.
Tool 1: Hyperscalers (comprehensive cloud suites)
These are the heavyweights designed for massive scale. They offer an end-to-end ecosystem where update management is just one module alongside analytics and storage. The former (AWS) excels in granular control via policies, whereas the latter (Azure) offers deep integration with enterprise systems.
- AWS IoT Device Management: The industry standard for organizing, monitoring, and remotely managing connected devices at scale.
- Microsoft Azure IoT Hub: ideal for enterprises requiring seamless integration with Active Directory and complex digital twin modeling.
Tool 2: FleetOps and container management
In 2026, many IoT devices function as micro-servers running containerized applications. Tools in this category focus on the DevOps experience for hardware, allowing you to push Docker containers or firmware updates seamlessly.
- Balena: The leader in container-based fleet management. It abstracts away the hardware complexity, allowing developers to push updates using standard git push workflows.
- JFrog Connect (formerly Upswift): A solution focused on Linux-based edge devices, offering lightweight remote access and update tools without the overhead of a full cloud suite.
- Golioth: A hardware-agnostic platform that bridges the gap between microcontroller firmware and the cloud, ideal for constrained devices using Zephyr RTOS.
Tool 3: Observability and machine health
You cannot manage what you cannot see. While basic platforms tell you if a device is online, observability tools predict when it will fail. This is critical for predicting maintenance needs and monitoring anomalies in Edge AI models.
- Datadog IoT Monitoring: Provides a unified view of device metrics alongside your backend infrastructure, allowing for end-to-end tracing of issues.
- Senseye PdM: Focused on industrial environments, it uses AI to analyze machine health and predict downtime before it occurs.
Tool 4: State management (digital twins)
Historically, we thought of backups as creating disk images. In modern IoT, we rely on device twins (or shadows). These are JSON documents stored in the cloud that reflect the desired and reported states of a device. If a device fails or is replaced, the new hardware simply syncs with the cloud twin to instantly restore its configuration.
Azure Digital Twins: Create comprehensive models of physical environments that preserve the state and history of entire fleets.
AWS Device Shadows: Persist the device’s last-known state so applications can interact with it even when offline.
Do you want to learn more? We can share our expertise!
Since 2012, SumatoSoft has been sharing its IoT expertise by delivering custom enterprise software and high-impact MVPs for startups and enterprises drive efficiency.
SumatoSoft offers industry-focused IoT solutions for healthcare, retail, manufacturing, banking industry, smart cities, and automotive domains. Examples include a fitness tracking system, a smart fridge sensors system, remote patient monitoring, warehouse automation, fleet management, robotics, smart traffic lights, and more. Every solution SumatoSoft builds comes with excellent security and scalability for future changes in terms of new features, fleet expansion, new users, and increased workload.
SumatoSoft IoT services include:
- End-to-end IoT application development
- Connectivity and fleet management
- Edge AI and data visualization
- IoT data analytics
- Strategic consulting and audits
Contact us for a free consultation about your IoT project.
FAQ
How do I ensure my IoT architecture is HIPAA compliant when using third-party cloud vendors?
HIPAA compliance in IoT requires a shared responsibility model. You must ensure all vendors in your stack (cloud, connectivity, and messaging) sign a Business Associate Agreement (BAA). Architecturally, you should isolate ePHI by partitioning operational telemetry from patient-linked data, enforcing role-based access control (RBAC), and maintaining centralized, auditable logs of all data access events.
When does IoT sensor telemetry fall within the scope of the GDPR?
Telemetry becomes personal data the moment it can be linked to an identifiable individual. In IoT, this often happens indirectly through device IDs, location traces, or usage patterns tied to a user account. Under GDPR, you must define a lawful basis for this data collection and implement technical enforcement for storage limitation (automated deletion) and data portability.
What are the must-have security controls for Industrial IoT (IIoT) under IEC 62443?
For industrial environments, auditors look for network segmentation (separating OT from IT), explicit trust boundaries at the gateway level, and authenticated update pipelines. The goal is to minimize the “blast radius” of a potential breach and ensure that remote maintenance access is strictly brokered and logged.
How can I manage data retention and deletion across a distributed IoT stack?
Retention must be enforced technically: you need to implement lifecycle rules at every storage point. For GDPR compliance, you must have automated workflows capable of executing “Right to Erasure” requests without disrupting the operational monitoring of the device fleet.
Let’s start
If you have any questions, email us info@sumatosoft.com